This Week’s [in]Security – Issue 150 | insecurity | Control Gap
Welcome to This Week’s [in]Security. Trending: Huawei and Crypto AG, Coronavirus, and Election...
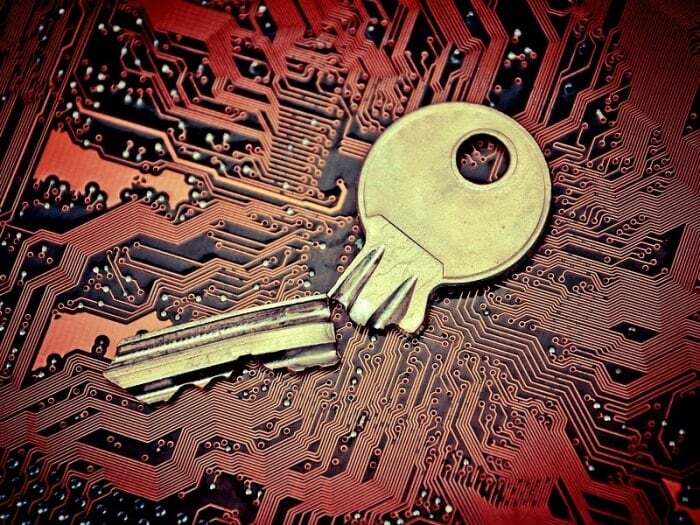
The SHA-1 cryptographic hash function was introduced in 1995. Weaknesses began to be discovered in 2005, and in 2011 NIST deprecated SHA-1. The use of SHA-1 web site certificates has been stopped. And now a practical collision attack against SHA-1 has been demonstrated by researchers who were able to create two different PDF files of the same length that produced an identical SHA-1 hash. The attack while practical is still a bit expensive, but I would expect speed improvements to emerge.
Hash functions like SHA-1 are used for validating the integrity of messages, software updates, and as unique signatures for data. The existence of a practical collision attack casts doubt on these applications.
Within the realm of PCI compliance, hash functions are used to render cardholder data unreadable (PCI DSS 3.4) and to validate the integrity of software source libraries and updates (PA-DSS and DSS software development). The use of hashes in PCI to render cardholder data unreadable is already subject to a number of restrictions and caveats to prevent attackers correlating truncated (partial) PAN with hashed.
How does the Shattered attack impact these uses of SHA-1?
If you are using SHA-1, should you be worried about your compliance? The answer, of course, depends upon how you are using it (see above).
I would expect that the PCI Security Standards Council will make some announcements and issue clarifications as a result of this.
Organizations relying upon SHA-1 that have not yet switched to a more secure hash like SHA-256 (or better SHA-3 standardized by NIST in 2012) should be accelerating this process and developing a strategy to address this. One of the first things you should be reaching out to your software vendors to find out what they are doing about this.
![This Week’s [in]Security – Issue 150 | insecurity | Control Gap](https://www.controlgap.com/hubfs/Imported_Blog_Media/camera-security-payment-700x467-Aug-13-2025-01-03-56-8537-PM.jpg)
 CG Blogger :
Feb 16, 2020 12:00:00 AM
CG Blogger :
Feb 16, 2020 12:00:00 AM
Welcome to This Week’s [in]Security. Trending: Huawei and Crypto AG, Coronavirus, and Election...
![This Week’s [in]Security – Issue 76 | insecurity | Control Gap](https://www.controlgap.com/hubfs/Imported_Blog_Media/phone-news-updates-700x467.jpg)
 CG Blogger :
Sep 10, 2018 12:00:00 AM
CG Blogger :
Sep 10, 2018 12:00:00 AM
Welcome to This Week’s [in]Security. We’ve collected and grouped together a selection of this...
![This Week’s [in]Security – Issue 130 | insecurity | Control Gap](https://www.controlgap.com/hubfs/Imported_Blog_Media/molehammer-2-700x573-Dec-21-2021-03-51-00-26-AM.jpg)
 CG Blogger :
Sep 30, 2019 12:00:00 AM
CG Blogger :
Sep 30, 2019 12:00:00 AM
Welcome to This Week’s [in]Security. This week: Big changes coming in PCI updates to DSS, P2PE...