Why Organizations Need to Become Crypto-Agile and What that Means
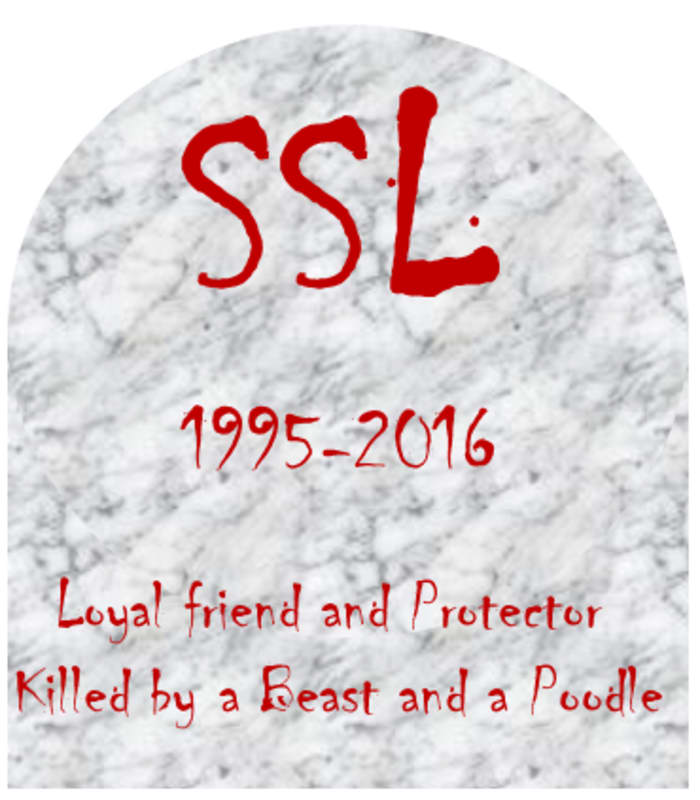
Cryptographic change is a reality. Since 2006, we have seen the sunset of WEP, SSLv2, RSA-1024, SSLv3 and early TLS. We know that Triple DES and...
11 min read
 David Gamey
:
Sep 23, 2021 10:07:00 PM
David Gamey
:
Sep 23, 2021 10:07:00 PM
According to some, quantum cryptography will revolutionize cryptography, kill our current ciphers, and reveal all our secrets. But if you're a risk manager, you're likely turned-off by claims of an impending crypto-apocalypse. You want to get past the hyperbole to something you can work with. You will want to know how likely this is, how to sort out facts from spin, what kinds of resources are available, how long you've got to prepare, and what preparation and planning do you need to do. You need to understand that quantum isn't just one thing, one risk, or the only risk. Join us as we break it all down for you.
Image Credit: Copyright Intel Corporation
Before we dig in, quantum computing isn’t the only driver of cryptographic change. Regardless of the eventual impact of quantum computing, organizations will still have to manage cryptographic changes. Or put another way, even if workable scalable quantum computers never happen, organizations will need to manage cryptographic change and should be looking at building cryptographic-agility programs.
Quantum Computers have tremendous potential and impact when, and if, we can get them working, overcoming technical challenges, and making them practical. In truth, we don't know when this will happen. We also don't know if we will encounter insurmountable obstacles or if there will be some new breakthrough that will make this happen sooner. However, uncertainty isn’t license for inaction. If we are going to address this pragmatically, we need to understand the playing field and start planning. There are a few things we can say:
Generally speaking, quantum computers are misunderstood and some of the cutting edge research is strange to say the least. Understanding something of the technology behind quantum computing is helpful to understanding its impact. However, for our purposes, we don’t want to get too far off the beaten path where quantum computing is entangled with physics and philosophy. Some of the Quantum Computing in Perspective references (below) may help. For a cryptographic perspective, Schneier makes a number of valid points but basically concludes that there is no quantum cryptography crisis and important work is being done to avoid one. Aaronson tackles explaining quantum computing, problem spaces, and enough physics and philosophy to put it all together and provide a glimpse of where this is going. There are some takeaways from all of this:
Many organizations try to exploit marketing buzz and hype with terminology like quantum, AI, ML, blockchain, etc. to gain attention, investors, and opportunities. Additionally, the science of quantum computing is advancing steadily. Consequently, it can be difficult to cut through the noise to get to the relevant information. Below, we break down specific applications of quantum technology that impact cryptography. Hopefully this will help your risk management teams put quantum cryptography into perspective and follow the developments.
In simplest terms, cryptographic-agility is the ability to manage risk and quickly deal with cryptographic change regardless if these are due to quantum computing or more conventional advances. Risk managers concerned with the impact of quantum computing will want to ensure they have a mature crypto-agility program that monitors areas of potential change including post-quantum cryptography and advancements in quantum computing.
The ultimate quantum cryptanalysis boogeyman is Shor's algorithm. Shor’s has the potential to crush public-key ciphers like RSA and ECC. Estimates in 2019 put a break time on 2048-bit RSA at 8 hours! Of course, the really BIG IF, is building a reliable enough quantum computer. Current machines not only fall dramatically short in qubits but they also can't keep it together long enough to complete the computations. Even if IBM builds their 1000 physical qubit machine in 2023, it will be far short of the 4096 logical qubits or 2M-25M physical qubits required to crack RSA-2048.
Even without quantum cryptanalysis, RSA is eventually doomed. As we move to longer and longer symmetric keys, RSA keys grow exponentially in length. With AES-128 commonly in use, RSA keys require 3072 bits for equivalent strength. AES-256 requires a whopping 15k bit long RSA key for equivalent strength. A paper described quantum resistant RSA with insanely long keys (the same paper also suggested a central key generation authority and created a bit of a controversy in the process).
ECC keys scale linearly but the cipher is still vulnerable to Shor’s algorithm. We could see ECC as an interim algorithm.
Quantum cryptanalysis will also have a major impact on symmetric cryptography. Grover's algorithm provides a huge advance but it's nowhere near the boogeyman that is Shor's. A practical implementation of Grover's means our AES-128 is no harder to break than a 64-bit key basically setting us back over 2 decades. Like Shor’s, Grover’s algorithm also requires a large number of logical qubits (2,953 for AES-128) and that 2 decade reset may not happen for a decade or more. Organizations worried about the long-term viability of 128-bit cryptography should get off AES-128 (and TDEA) as soon as possible. Standards bodies could easily deprecate 128-bit keys. AES-256 will remain as solid post quantum as AES-128 is today. If new 512-bit ciphers are needed, they could be developed going forward.
Grover’s algorithm also impacts pre-image and collision attacks on MACs and Hashes in the same way as ciphers like AES. However, there are already a number of good non-quantum reasons to reconsider many hashing use-cases (See Crypto-Agility).
If Grover’s is as good as it gets, we should not be worried. Of course, cryptographic-agility programs will need to move to stronger symmetric algorithms and pay attention to the retention of old cryptograms derived from shorter keys.
Cryptographers and standards bodies aren't waiting for practical large scale quantum computing to become reality. Work is proceeding to replace the Public-Key encryption and digital signature algorithms are impacted by Shor's algorithm. As noted, symmetric key encryption is not considered at risk.
Quantum key distribution (QKD) is here today. It provides a method of remotely agreeing keys that provably cannot be eavesdropped without detection. It's very interesting and serves some niche applications. But how practical is it? Where does it fit?
While the keys may be agreed securely, can they be held and used securely? A challenge to the general use of this technology is that the keys are still available to classical technologies. And if the keys are used for classical ciphers, is there any real advantage in general use cases? Most organizations aren’t going to have QKD kit any time soon.
We can also, foresee potential jurisdictional and cross-border issues arising once this technology can be made to work at really long range.
A recent and interesting development is the use of quantum computers for random key generation. While we haven’t seen a lot on this it’s worth noting that we already have random sources that outperform pseudo-random-number-generators. And as some of the challenges to using this for general applications are similar to QKD, it’s hard to see this as more than fitting a special use-case.
Cryptography is not the only application for quantum technologies and there other interesting uses. As with any new technology (e.g. artificial intelligence, machine learning, blockchain) the interest in quantum also generates it's share of spin, hype, and misleading or false claims. Fortunately, the field of quantum cryptography gets a lot of scrutiny and reliable answers are available.
Our annotated references broken down by topic. Many of the referenced articles have been covered in our weekly [In]Security News summaries https://controlgap.com/blog?tab=insecurity
Cryptographic-Agility:
Quantum Computing in Perspective:
Shor’s Algorithm:
Grover's Unstructured Search Algorithm:
Post-Quantum (Quantum Resistant) Cryptography:
Quantum Key Distribution:
Quantum Key Generation:
Quantum Computers:
Some are other “quantum technologies” not covered nor directly relevant to this article:

Cryptographic change is a reality. Since 2006, we have seen the sunset of WEP, SSLv2, RSA-1024, SSLv3 and early TLS. We know that Triple DES and...

If you’ve been struggling with keeping up with various SSL vulnerabilities and planning an orderly cutover to TLS then the recent announcement by...
1 min read
The PCI Security Standards Council today published the expected update to PCI releasing these documents including some specific migration guidance: